Outbound-only
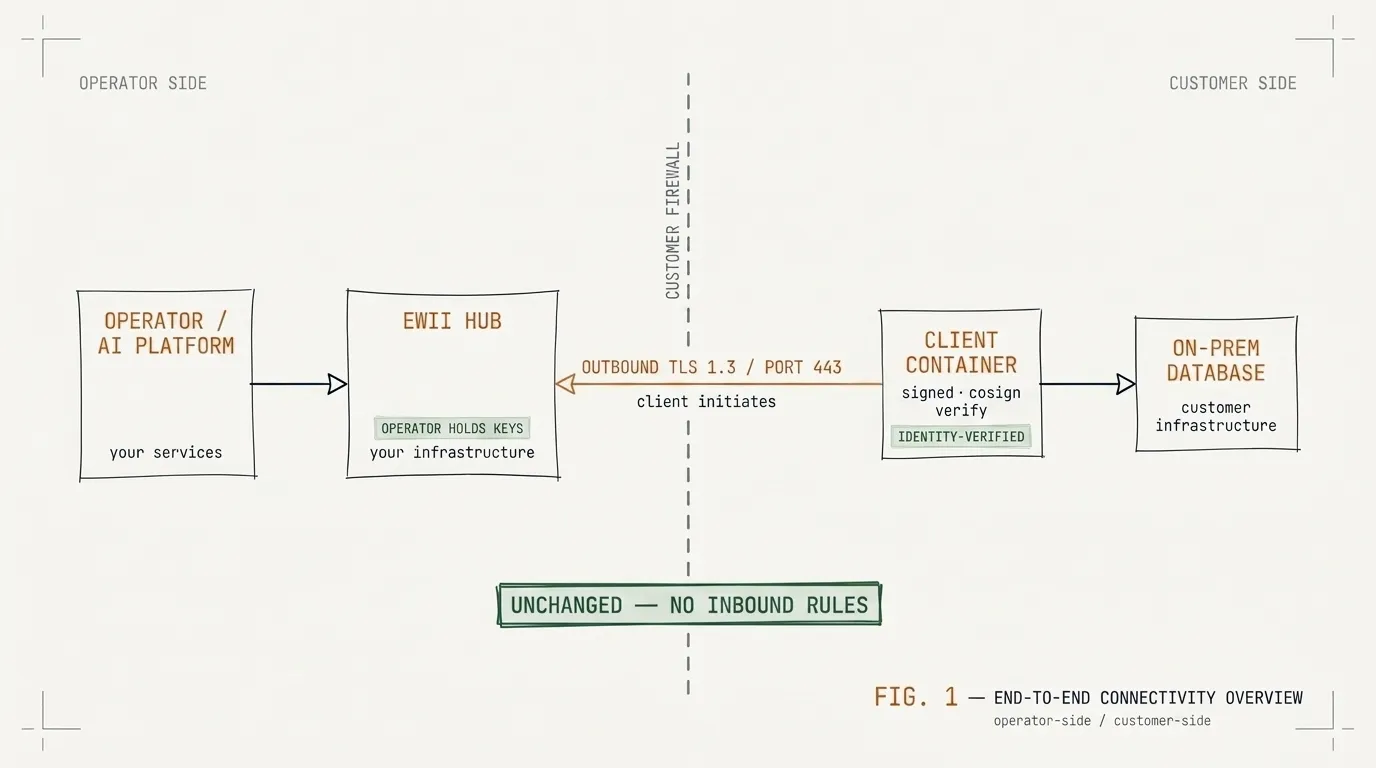
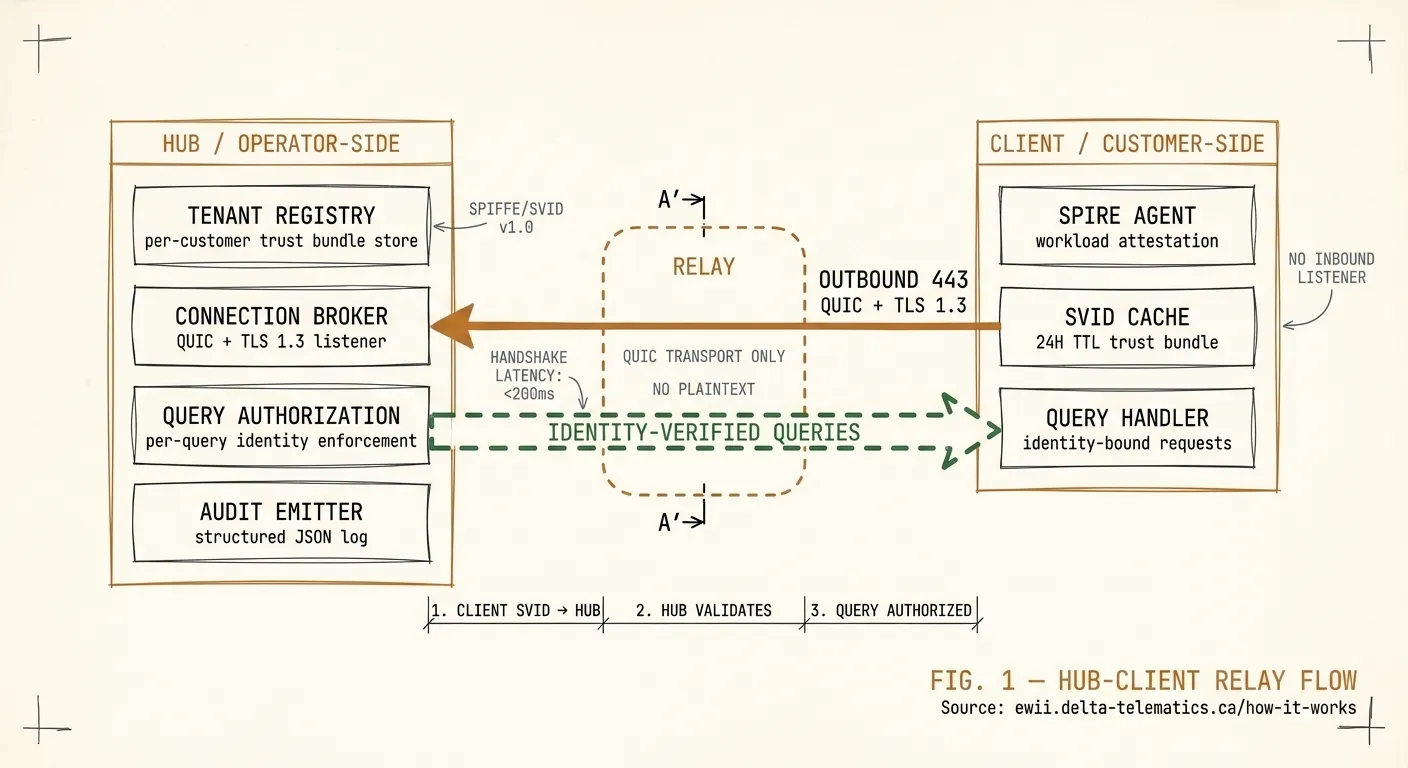
Your customers’ firewalls don’t change. Ewii’s Client opens a single outbound connection on port 443. No inbound rules, no port-forwarding, no DMZ.
EWII SECURE MCP VPN
Reach your customers’ on-prem databases without firewall changes, credential exposure, or VPN hardware. Hub on your side. Signed Client on theirs. Encrypted, identity-verified traffic over outbound port 443.
Built on
Your customers’ firewalls don’t change. Ewii’s Client opens a single outbound connection on port 443. No inbound rules, no port-forwarding, no DMZ.
SPIFFE workload identity. Short-lived X.509 certificates. No shared secrets, no static API keys. Every request is identity-verified at the workload boundary.
Canadian datacenters. Protected B-aligned. Signed tenant-specific Client containers with Cosign. Defense-in-depth encryption your auditor can read.
HOW IT WORKS
FOR YOU, THE OPERATOR
White-labelable. SLA-backed. We start every engagement with an Architecture Review so your team and ours agree on the deployment shape before you commit.
FOR YOUR CUSTOMERS
Their data stays on their infrastructure. Their security team approves it once. We wrote this page so an operator can copy the URL into their own change-management package.
USE CASES
ITSG-33-aligned, Canadian KMS, security-questionnaire-ready.
FINANCIAL SERVICESCardholder-data isolation, end-to-end audit trail, defense-in-depth.
HEALTHCAREAir-gapped database access, BAA-ready Hub, encryption in transit and at rest.
MOREEnergy, telecom, defense — talk to us about your sector.