Compare
Ewii vs. Tailscale
Tailscale is one of the best-engineered networking products of the last decade. The control plane is excellent, the WireGuard data plane is fast, and the operational story for small-to-medium teams is hard to beat. If your problem is “I have engineers in three offices and a homelab and I want them on the same logical network,” use Tailscale.
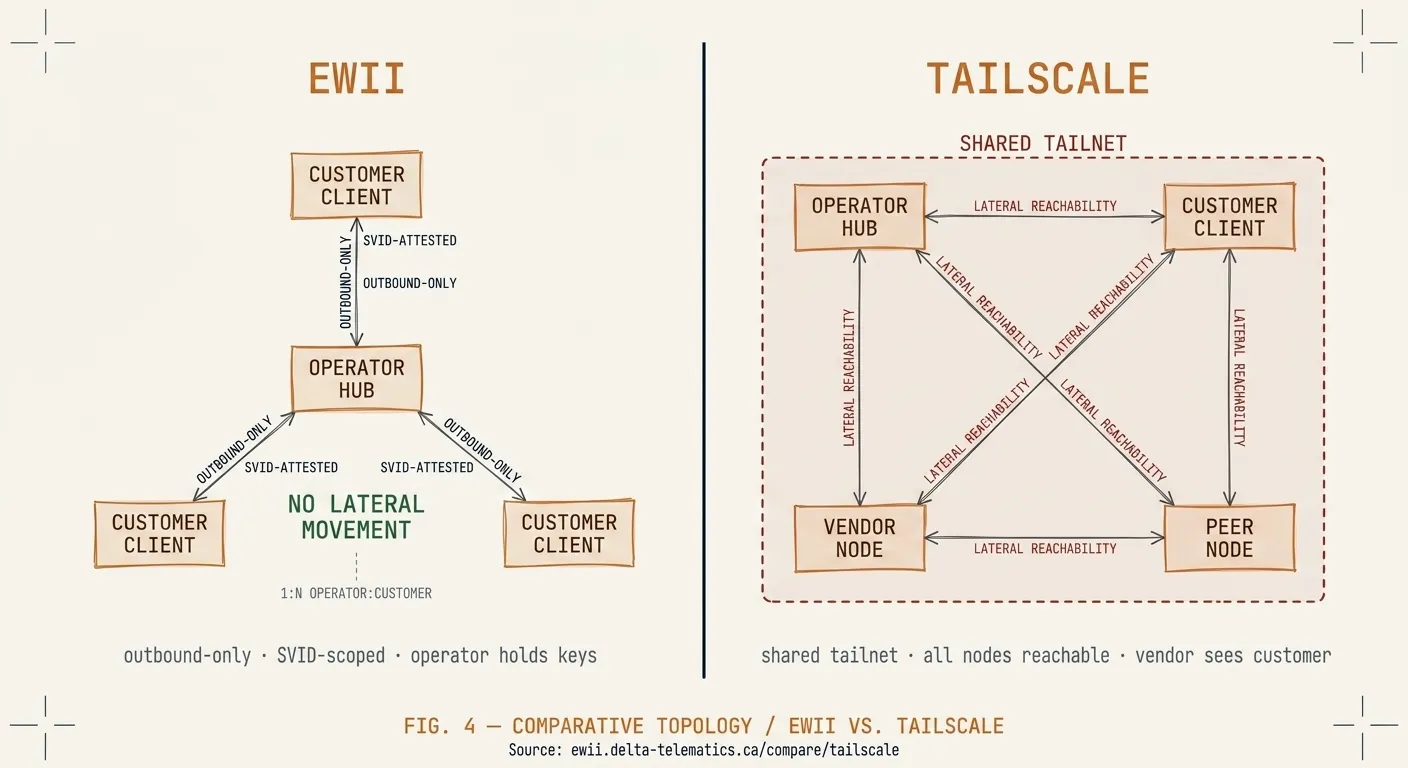
The Ewii use case is not that. Ewii is one-way connectivity from a single operator (you, the AI or SaaS vendor) to many customers. The customers do not join your network and you do not join theirs. Identity flows in one direction. Audit flows in one direction. The deployment shape is different from a mesh, and the security review is different.
Topology
| Dimension | Ewii | Tailscale |
|---|---|---|
| Network shape | One operator → many customers (hub-and-spoke) | Mesh between consenting peers |
| Identity model | SPIFFE workload identity per Client | Tailscale identity per node (user or service) |
| Customer admin involvement | Customer security team approves Client image | Customer admin enrolls each node into your tailnet |
| Network reachability | Application-layer query path only | Subnet-level routing (configurable) |
| Audit boundary | Operator-side; per-query identity-bound | Tailnet-wide; per-connection |
| Multi-tenant separation | SPIFFE trust bundle per customer | Per-tailnet (one tailnet per customer is common) |
Mesh ≠ operator → customer
Tailscale’s threat model assumes consent on both ends. To put a customer’s database server on your tailnet, the customer’s admin enrolls a node into your tailnet — or, more commonly, you join theirs. Either way, both parties are materially participating in a single network with shared reachability semantics.
That is structurally inappropriate for the operator-to-customer use case. The customer should not have to grant you network-level access to a service in order to let your AI product call it. They should be able to grant you application-level access to one specific query path, with one specific identity, and revoke it without negotiating with you.
Ewii’s model is: the customer runs a Client container next to the database. The Client opens an outbound connection to your Hub. Your Hub authenticates the Client’s SPIFFE SVID. Application-layer queries flow over that one connection. There is no shared network. There is no enrollment of customer infrastructure into your tailnet. There is no admin-level relationship.
The procurement conversation
A hospital security reviewer evaluating “we’d like to put your AI tool on our tailnet” has to think about subnet routing, lateral-movement surface area, the tailnet’s ACL model, and what happens when the AI vendor is acquired or breached. None of these are unanswerable questions, but they are not the questions the procurement team wanted to spend time on.
The same reviewer evaluating “we’ll run a signed Client container next to the
database, it makes one outbound connection on 443, and it speaks one
identity-verified query interface” has a much shorter list. They have to
verify the Client image (signed with Cosign — they can run cosign verify
themselves), confirm the egress port (443), and review the query interface
contract. The question becomes a code review, not a network architecture
debate.
When Tailscale is the right answer
If you and your customer have engineers who already think in tailnet terms, and the relationship is operationally peer-like — for example, a managed infrastructure provider who needs deep network access into a customer environment — Tailscale is a fine choice and Ewii does not displace it.
If the relationship is “we are an AI vendor; the customer wants to run our product against their data without giving us network-level access” — that is the Ewii use case, and a mesh VPN is the wrong shape for it.