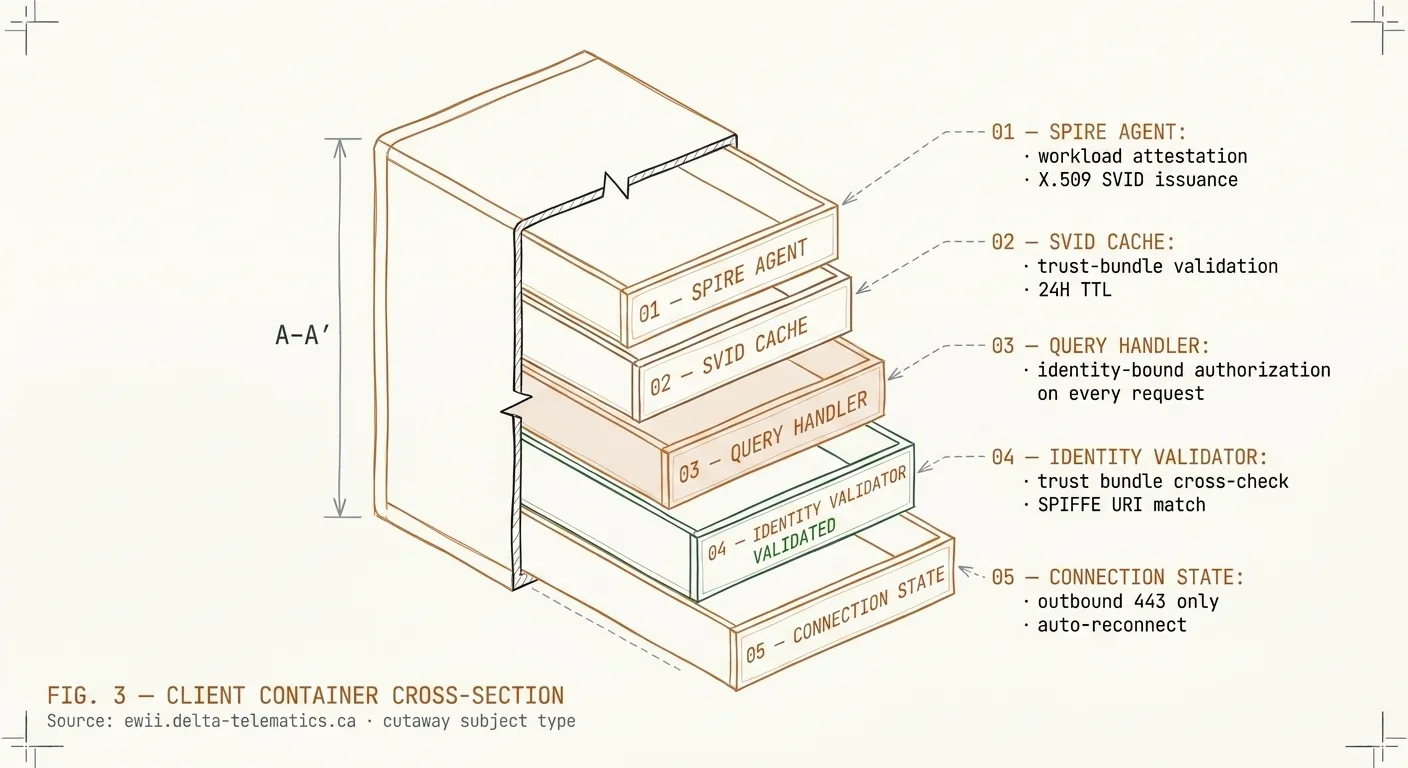
What you’ll deploy
A single signed container, roughly 80 MB, that runs on any Linux host with an outbound
internet connection. It runs as a non-root user. It does not require kernel modules,
privileged capabilities, or a host-network namespace. Image signature can be verified
before deployment with cosign verify.