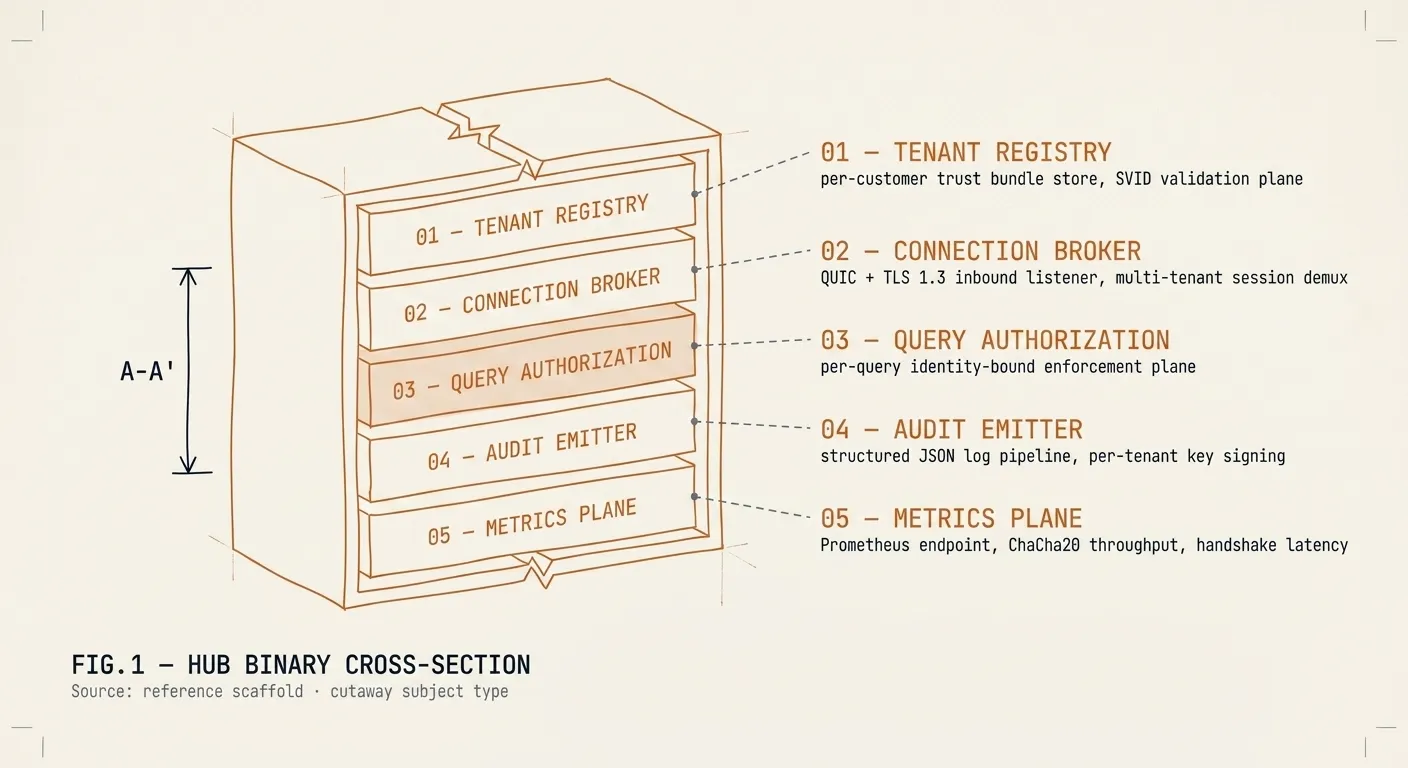
Hub deployment characteristics
The Hub runs as an OCI container in your infrastructure: your VPC, your Kubernetes cluster, your bare-metal. Resource footprint is moderate — a single Hub instance handles thousands of concurrent Client connections. We provide the binary, the image signed with Cosign, the deployment manifest, and the operational runbook. Your team owns the rollout. We back you up.