Banks, insurers, and payment platforms can’t move cardholder data. They also can’t afford to be the slow yes in their own AI roadmap. Ewii is the connectivity layer that lets your analytics or AI platform reach the data without expanding the cardholder data environment (CDE).
Cardholder-data isolation
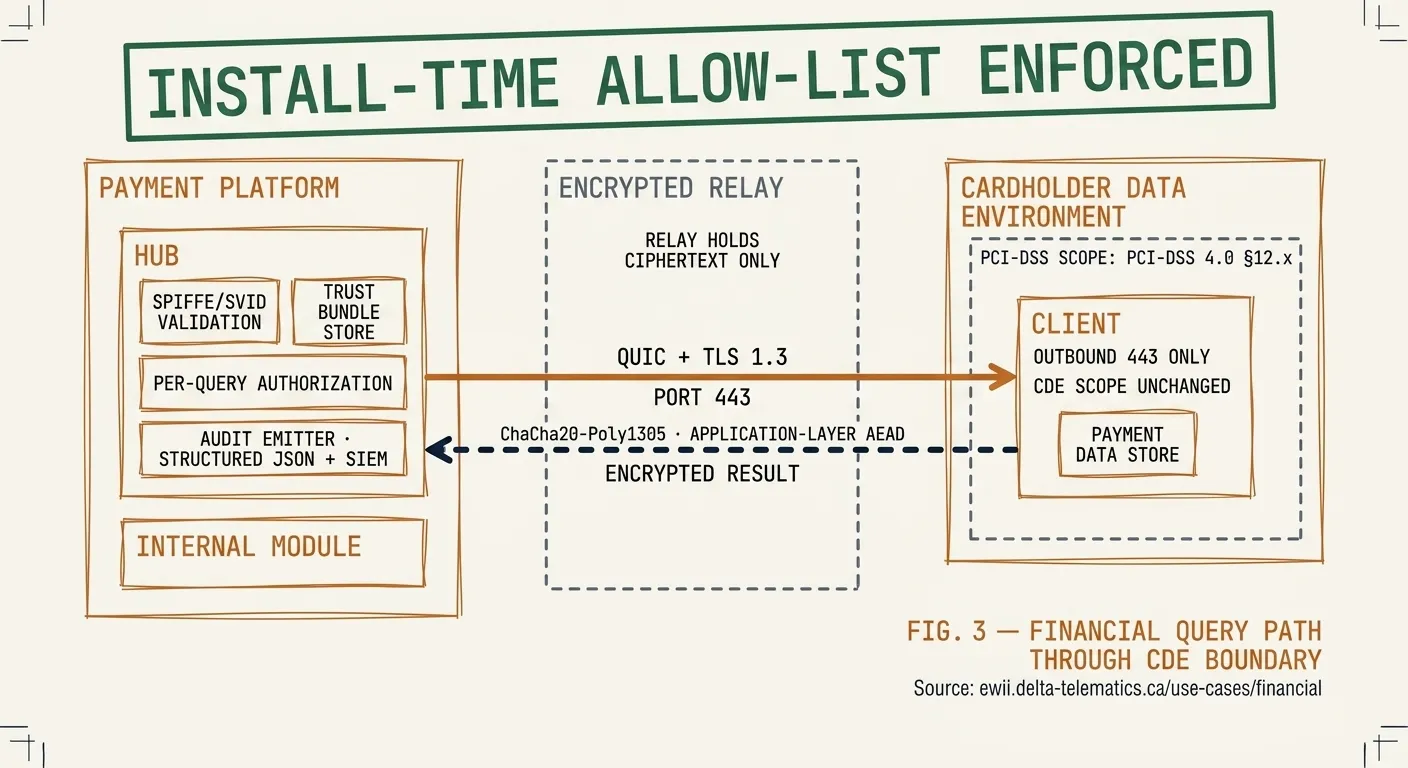
The Client container is constrained at install to the exact endpoint(s) it’s allowed to reach. The install-time allow-list is the only set of destinations it dials; nothing outside it is reachable. From PCI-DSS’s perspective, the Client is a network-isolated workload that initiates outbound traffic to a single authenticated relay — not a reduction in the CDE perimeter, but an auditable extension of it.
End-to-end audit trail
Every connection is logged with: timestamp, source workload SVID, destination, bytes transferred, duration, and the result of the certificate validation. Logs are structured JSON, suitable for forwarding to your SIEM. The Hub also emits Prometheus metrics for connection-level operations and certificate-rotation events. PCI auditors have asked us for sample logs and we’ve handed them over without redaction — nothing we log is sensitive.
Defense-in-depth encryption
TLS 1.3 at the transport layer (QUIC). ChaCha20-Poly1305 at the application layer. X25519 ephemeral key exchange. HKDF-SHA256 key derivation. A compromised relay cannot read payloads. A compromised Hub cannot impersonate a Client. A compromised Client cannot read another tenant’s traffic. The cryptographic primitives are named and documented; nothing is proprietary.
Sub-second revocation latency
Stop the Client; the Hub detects the lost connection within seconds, blacklists the SPIFFE certificate, and refuses re-handshake even if the Client comes back. Operator-side revocation is similarly fast. For financial workloads where access revocation is a regulatory requirement, this matters.
Talk to an architect
Bring your existing PCI-DSS scope diagram. We’ll show you exactly which controls Ewii moves, which it doesn’t, and what the auditor will ask. 60 minutes. No sales pitch.