Hospitals, payors, and clinical-AI platforms share a constraint that’s easy to articulate and hard to satisfy: PHI cannot leave the network. AI tools that need to query PHI — for clinical decision support, claims processing, population analytics — either move PHI (unacceptable) or run inside the network (operationally painful). Ewii is the third option.
Air-gapped database access
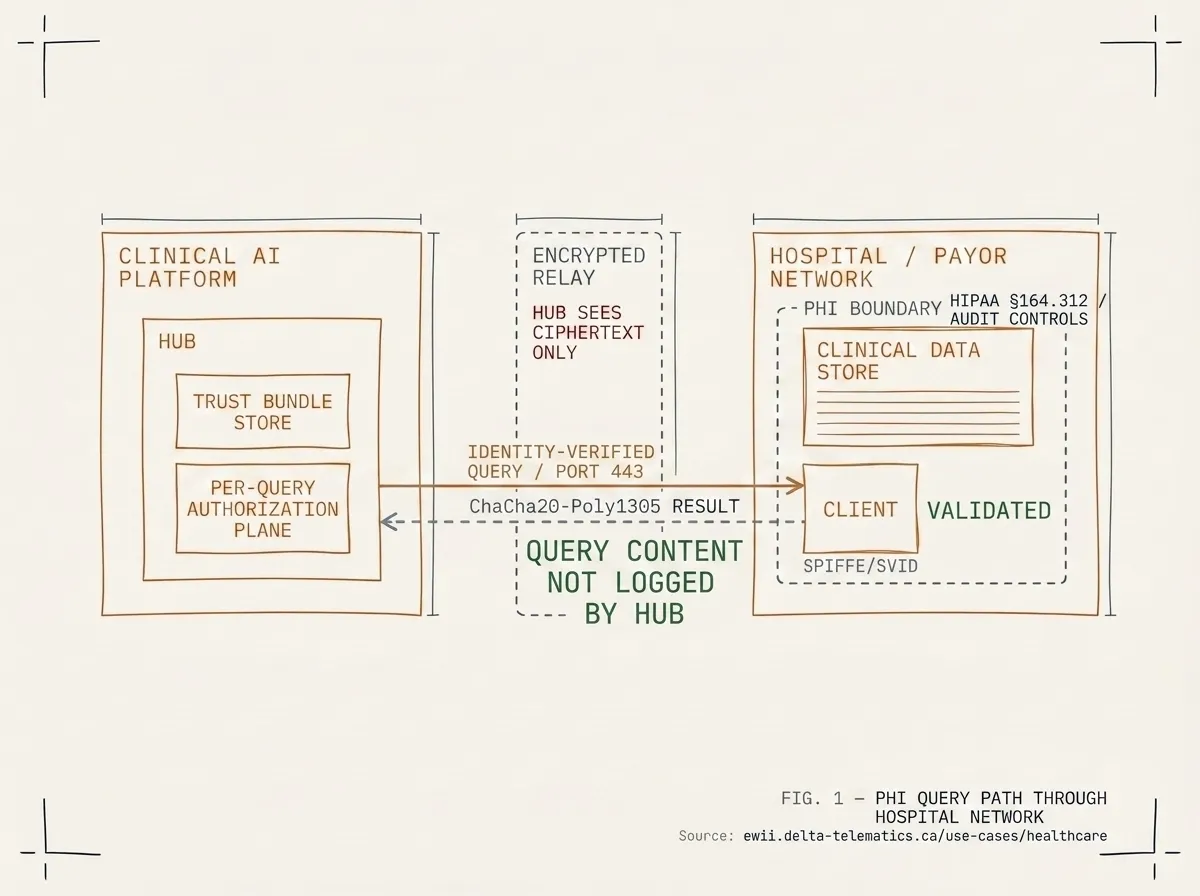
The clinical-data store stays where it is. The Client container, deployed inside the hospital or payor network, is the only thing that touches it. Identity-verified queries flow outbound to the operator’s Hub; query results return on the same connection. PHI never crosses the network boundary in a form the operator can store. The Hub sees ciphertext only.
PHI never leaves the network
Application-layer encryption (ChaCha20-Poly1305) is end-to-end between the Client and a workload-bound Hub endpoint. The Client decrypts query results in the customer’s memory; the Hub never sees plaintext PHI. Logs from the Client capture metadata (query identifier, timestamp, size) but not query content. We can show your privacy officer the exact set of fields the Hub side observes.
BAA-ready Hub deployment
For US healthcare deployments, our standard Hub posture is BAA-ready: the operator runs the Hub under a BAA with us, and we, in turn, are willing to enter into a BAA with each operator that needs one. For Canadian healthcare deployments, we align to PHIPA and provincial equivalents (BC PIPA, Quebec’s Loi 25). Our Trust Center pack includes a sample BAA and a PHIPA mapping.
Identity-verified queries replace network-level access
Today, your operator’s service account probably has network-level read access to the clinical database. Tomorrow, with Ewii, it has identity-verified per-query access — the Client enforces what queries are allowed, the Hub validates the identity at every connection, and every query is logged. Network-level access becomes per-query access. Audit becomes possible.
Talk to an architect
Bring your privacy officer if you can. We’ll show you the data-flow diagram, the BAA shape, the audit trail your auditor will see, and what the rollout looks like. 60 minutes.